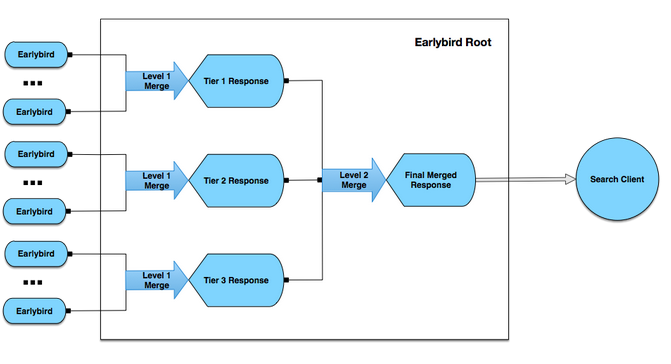
Since that first simple Tweet over eight years ago, hundreds of billions of Tweets have captured everyday human experiences and major historical events. Our search engine excelled at surfacing breaking news and events in real time, and our search index infrastructure reflected this strong emphasis on recency. But our long-standing goal has been to let people search through every Tweet ever published.
This new infrastructure enables many use cases, providing comprehensive results for entire TV and sports seasons, conferences (#TEDGlobal), industry discussions (#MobilePayments), places, businesses and long-lived hashtag conversations across topics, such as #JapanEarthquake, #Election2012, #ScotlandDecides, #HongKong,#Ferguson and many more. This change will be rolling out to users over the next few days.
Tag Archives: twitter
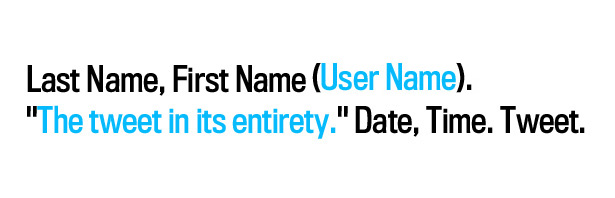
How Do You Cite a Tweet (MLA Style) in an Academic Paper?
The Modern Language Association likes to keep up with the times. As we all know, some information breaks first or only on Twitter and a good academic needs to be able to cite those sources.
So, the MLA has devised a standard format that you should keep in mind when citing a tweet.
Here it is…
How Do You Cite a Tweet in an Academic Paper? – Alexis Madrigal – Technology – The Atlantic.
CIA following Twitter, Facebook
Beware the ‘vengeful librarians’ [which is pretty much an oxymoron, if you ask me]
In an anonymous industrial park in Virginia, in an unassuming brick building, the CIA is following tweets — up to 5 million a day.
At the agency’s Open Source Center, a team known affectionately as the “vengeful librarians” also pores over Facebook, newspapers, TV news channels, local radio stations, Internet chat rooms — anything overseas that anyone can access and contribute to openly.
via AP Exclusive: CIA following Twitter, Facebook – Yahoo! News.
Library of Congress Builds Twitter Archive
Library of Congress is now archiving every single tweet that has ever been tweeted since the inception of Twitter in 2006. This will be a huge project since there are billions and billions of tweets to archive.
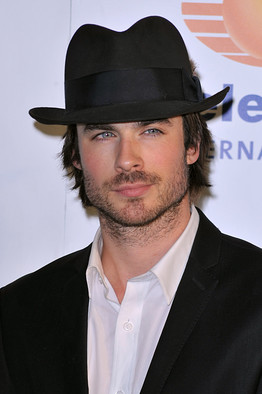
A Question of Authority: How Does Twitter Verify [Celebrity] Accounts?
Twitter has 175 million users and counting and only select, mostly high-profile people are granted “verified†status. How are verified users vetted? Twitter refused to explain the process, saying via e-mail, “we continue to very selectively verify accounts most at risk for impersonation on a one-off and highly irregular basis.â€
How Does Twitter Verify Celebrity Accounts? – Speakeasy – WSJ.